GHSA-FJ52-5G4H-GMQ8
Vulnerability from github – Published: 2026-04-14 23:39 – Updated: 2026-04-14 23:39
VLAI?
Summary
pyLoad's Session Not Invalidated After Permission Changes
Details
Summary
The pyload application does not properly invalidate or modify sessions upon changes made to a user's permissions.
Details
Whenever an administrator changes the permissions a specific account has, they do not expect that account still being able to access data that their new permissions do not allow. This is not the case for the pyload application, as a user with a valid session can still perform the actions.
PoC
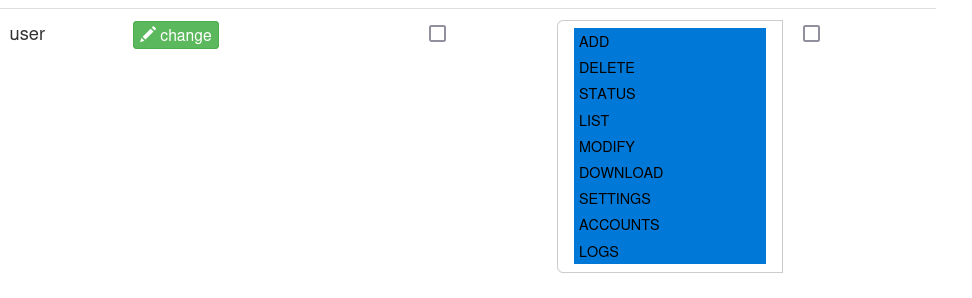
Take a user with all the permissions, as shown below.
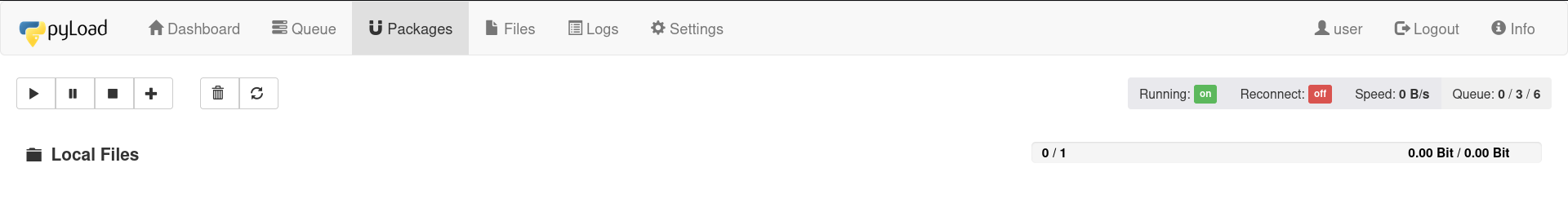
We now log in as this user.
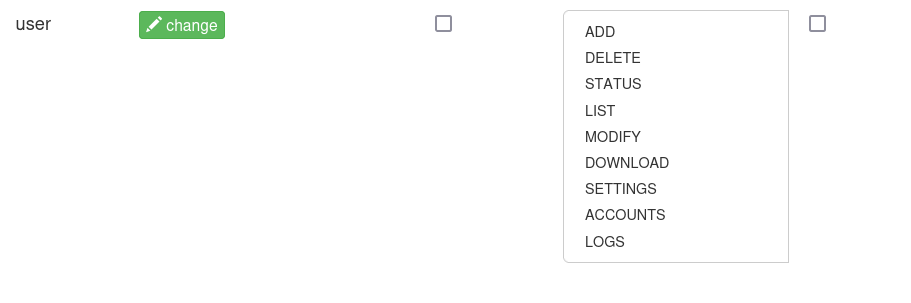
Let us now take away all the permissions.
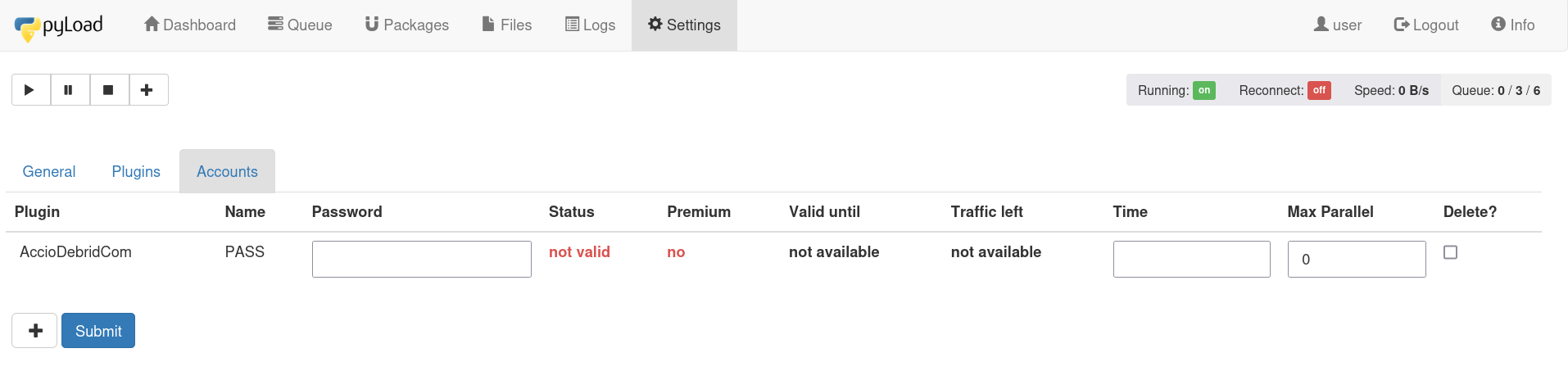
The logged in session can still be used to access everything in the application.
Impact
Should permissions be taken away, then the user is expected not to be able to execute the actions belonging to those actions anymore.
Severity ?
{
"affected": [
{
"package": {
"ecosystem": "PyPI",
"name": "pyload-ng"
},
"ranges": [
{
"events": [
{
"introduced": "0"
},
{
"last_affected": "0.5.0b3.dev97"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [],
"database_specific": {
"cwe_ids": [
"CWE-613"
],
"github_reviewed": true,
"github_reviewed_at": "2026-04-14T23:39:25Z",
"nvd_published_at": null,
"severity": "LOW"
},
"details": "### Summary\nThe `pyload` application does not properly invalidate or modify sessions upon changes made to a user\u0027s permissions.\n\n### Details\nWhenever an administrator changes the permissions a specific account has, they do not expect that account still being able to access data that their new permissions do not allow. This is not the case for the `pyload` application, as a user with a valid session can still perform the actions.\n\n### PoC\nTake a user with all the permissions, as shown below.\n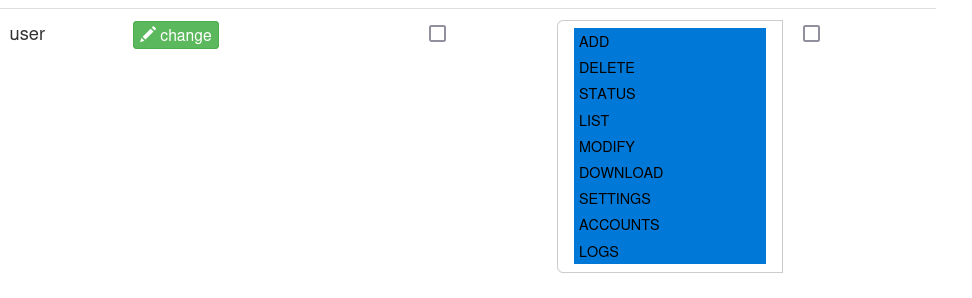\n\nWe now log in as this user.\n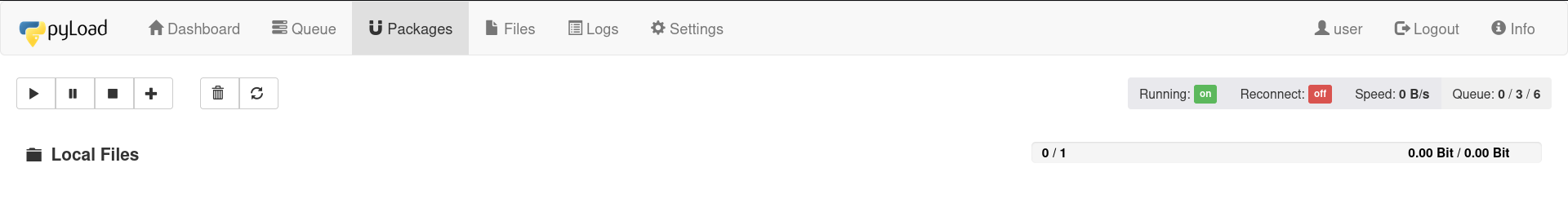\n\nLet us now take away all the permissions.\n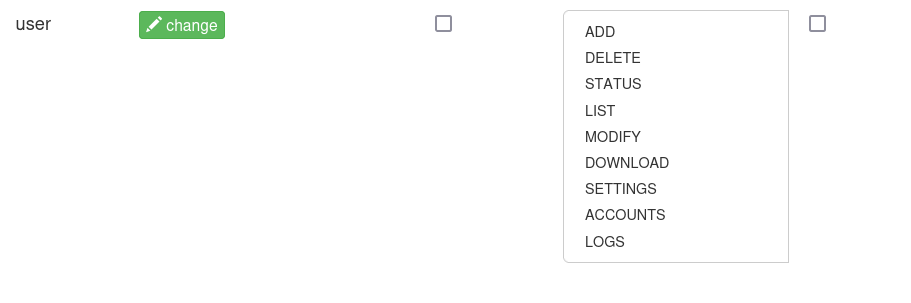\n\nThe logged in session can still be used to access everything in the application.\n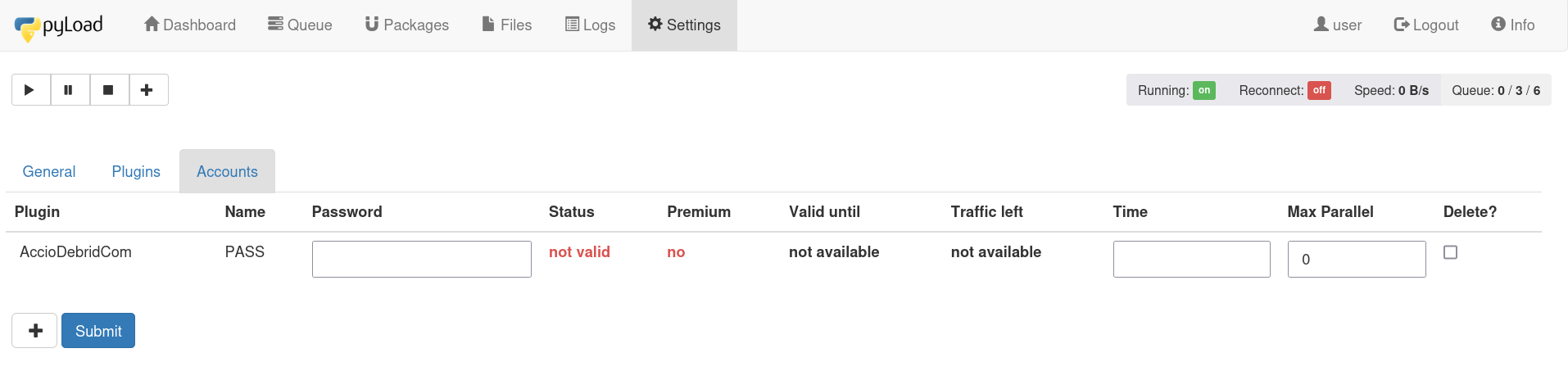\n\n### Impact\nShould permissions be taken away, then the user is expected not to be able to execute the actions belonging to those actions anymore.",
"id": "GHSA-fj52-5g4h-gmq8",
"modified": "2026-04-14T23:39:25Z",
"published": "2026-04-14T23:39:25Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/pyload/pyload/security/advisories/GHSA-fj52-5g4h-gmq8"
},
{
"type": "WEB",
"url": "https://github.com/pyload/pyload/commit/e95804fb0d06cbb07d2ba380fc494d9ff89b68c1"
},
{
"type": "PACKAGE",
"url": "https://github.com/pyload/pyload"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:L/VI:L/VA:N/SC:N/SI:N/SA:N/E:P",
"type": "CVSS_V4"
}
],
"summary": "pyLoad\u0027s Session Not Invalidated After Permission Changes"
}
Loading…
Loading…
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…